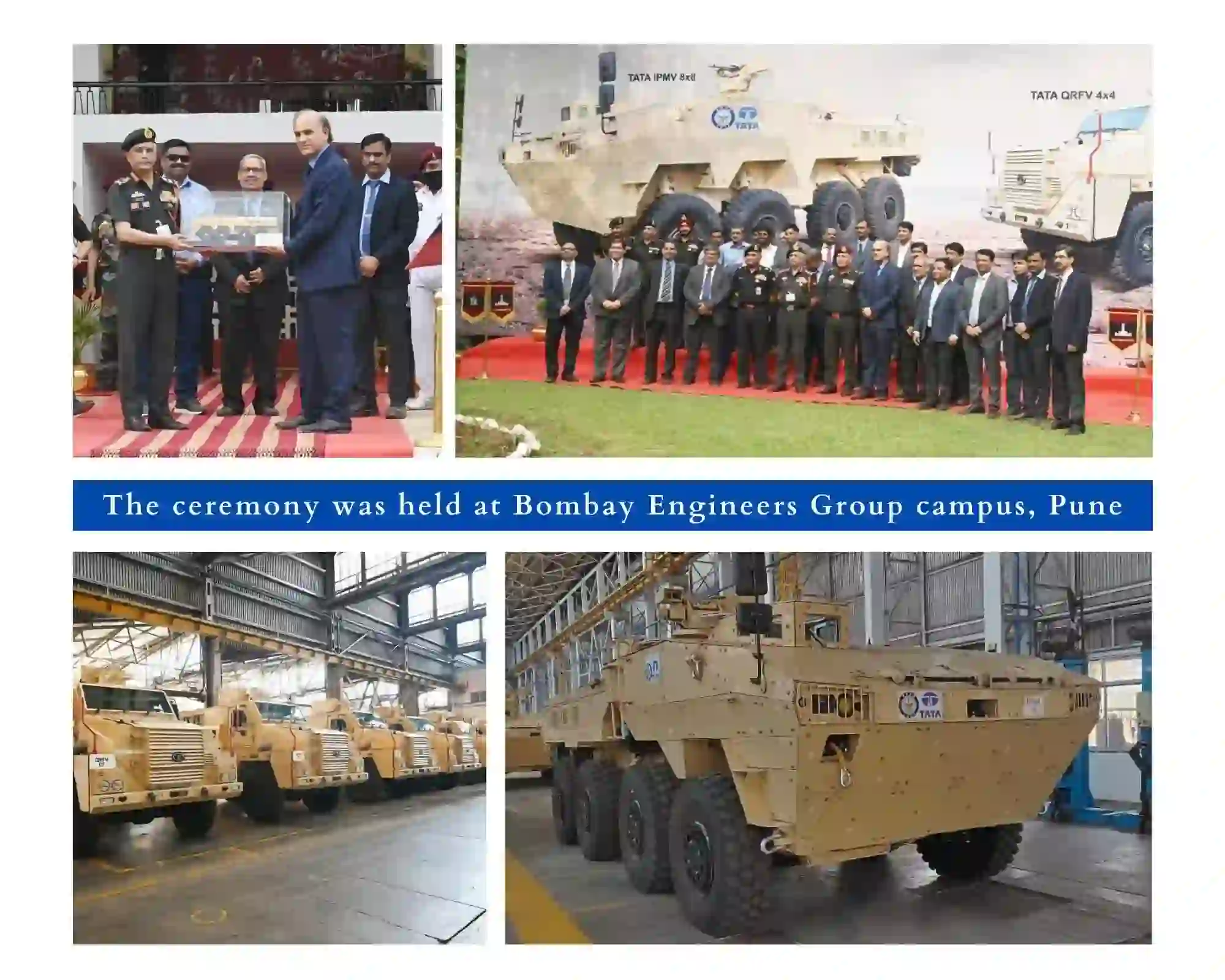
Tata Mine Protected Vehicle
It is fully designed and manufactured in-house and delivers an unmatched combination of proven performance in the harshest operating conditions along with low maintenance and lifecycle cost. The Tata MPV is an “in-service” platform with the Indian Army.

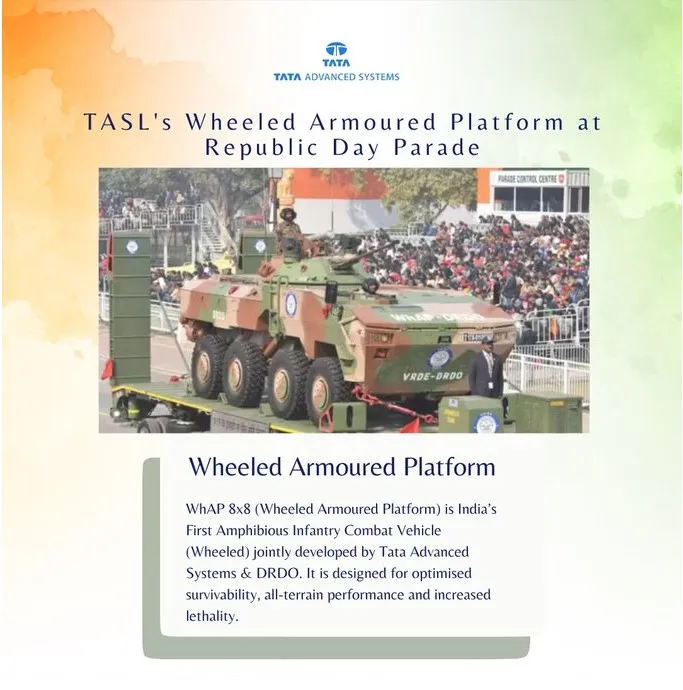
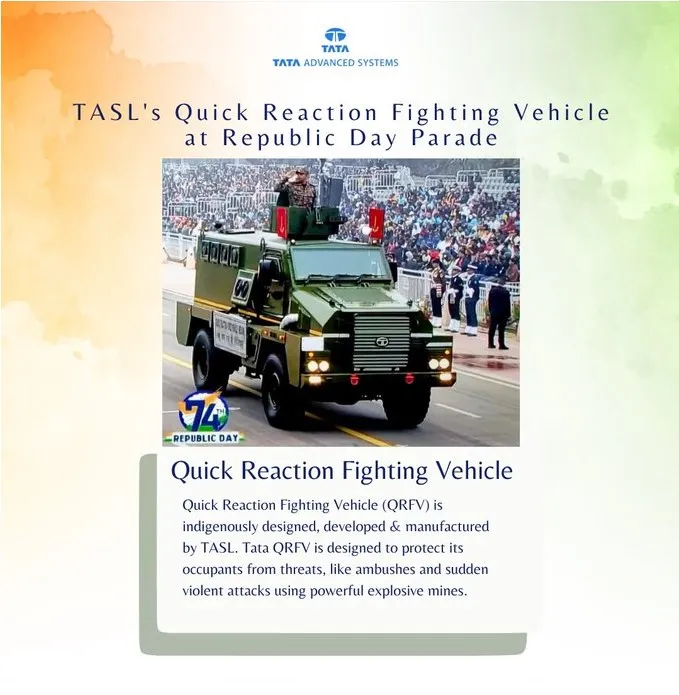
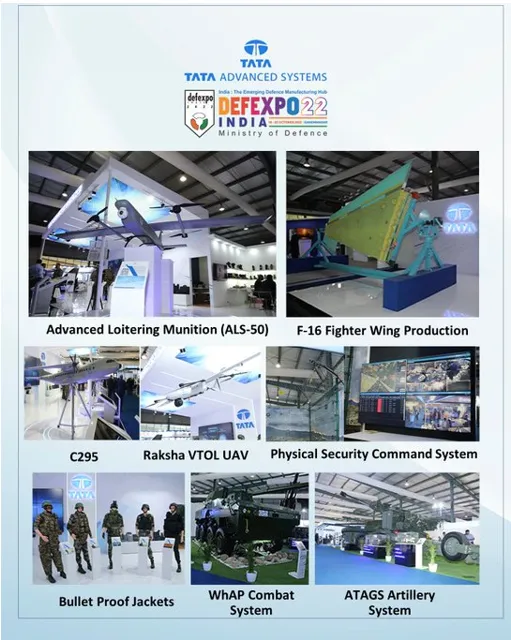
TATA 8X8 WhAP
TASL has indigenously designed and developed, with DRDO, a Wheeled Infantry Combat Vehicle, with amphibious capability. It is an all-terrain and climate system that has been procured by the Indian Army.

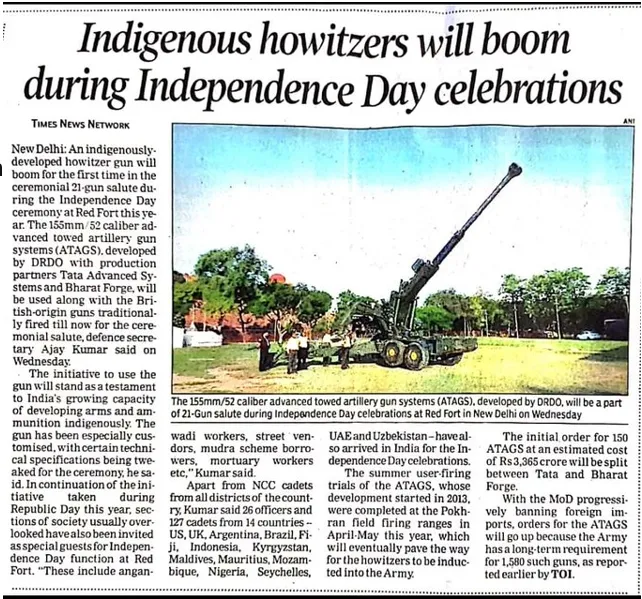
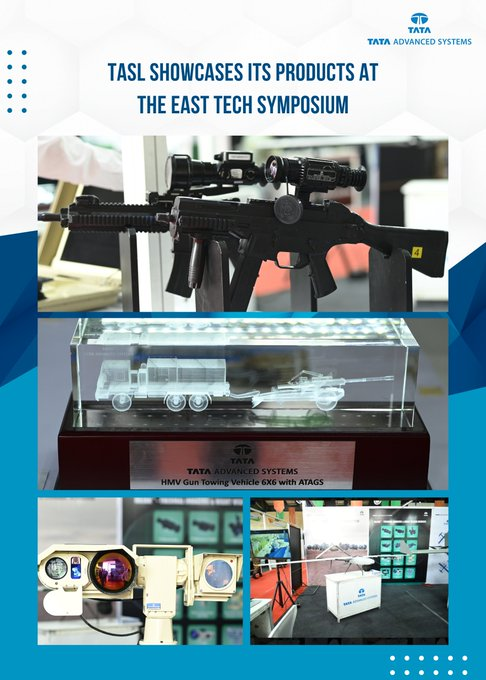
Advanced Towed Artillery Gun Systems
TASL has indigenously designed and developed, with DRDO, a 155mm x 52 Calibre Howitzer with maximum range of 45+ Kms. It has an electric drive and is a fully automatic gun that is reliable in all-terrain and climate conditions.

Surface Surveillance Radar
Manufacturing, assembly & integration since 2017 in Defence division, Noida Plant

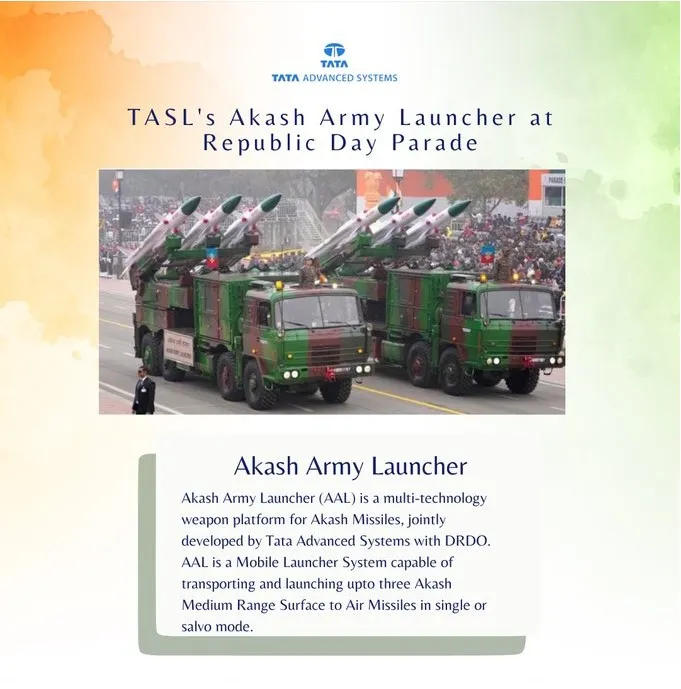
Missile Launchers
TASL indigenously designs, develops and produces missile and rocket launchers (like Akash, MRSAM, TCT Agni, ULAD, Pinaka) for Indian Armed Forces

Command & Control Systems
Design, Development and Production of Mission Centres and Combat Management Systems


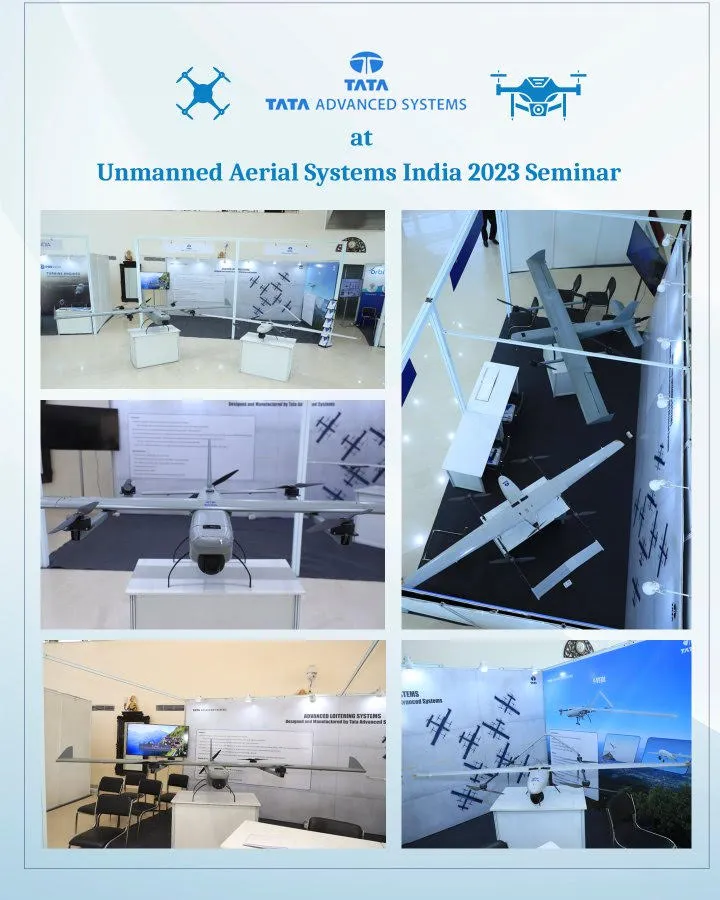
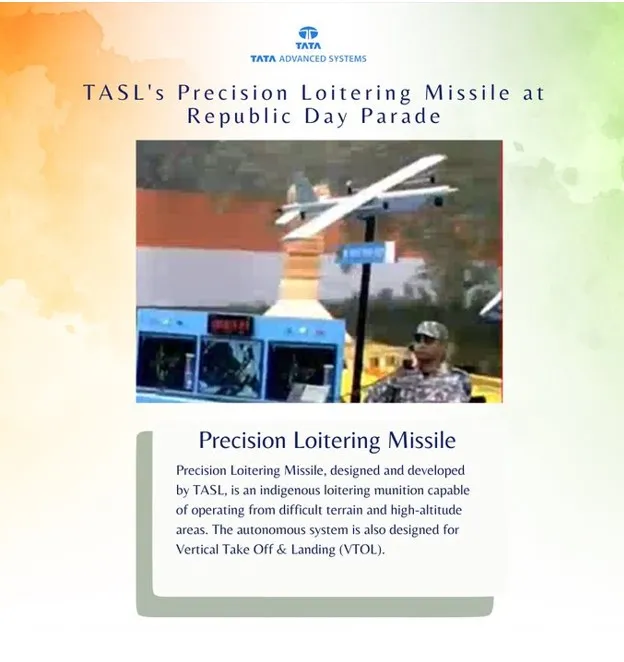
Airborne Platforms and Systems
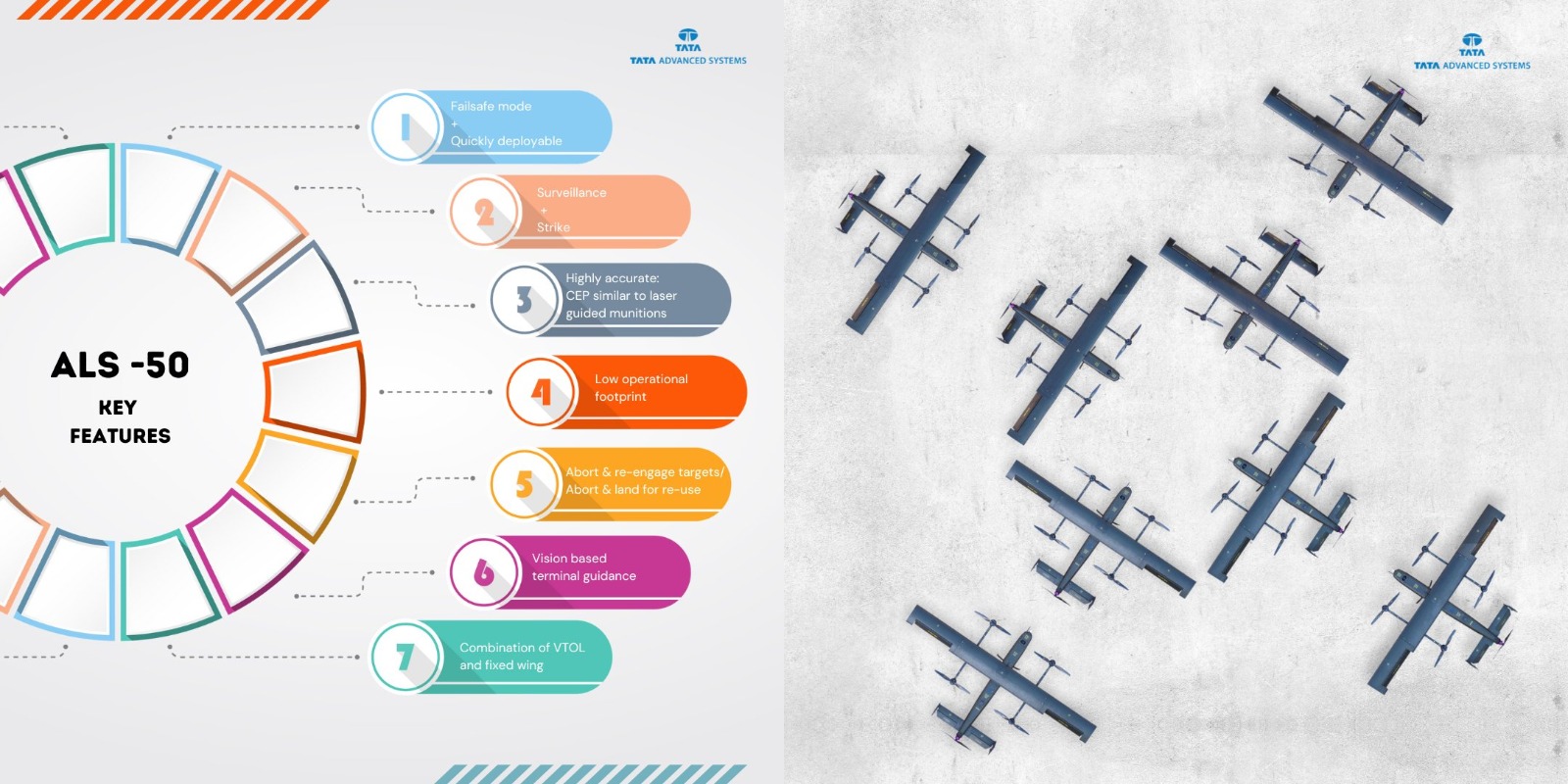
TASL's Airborne Platforms & Systems Division is developing advanced UAVs

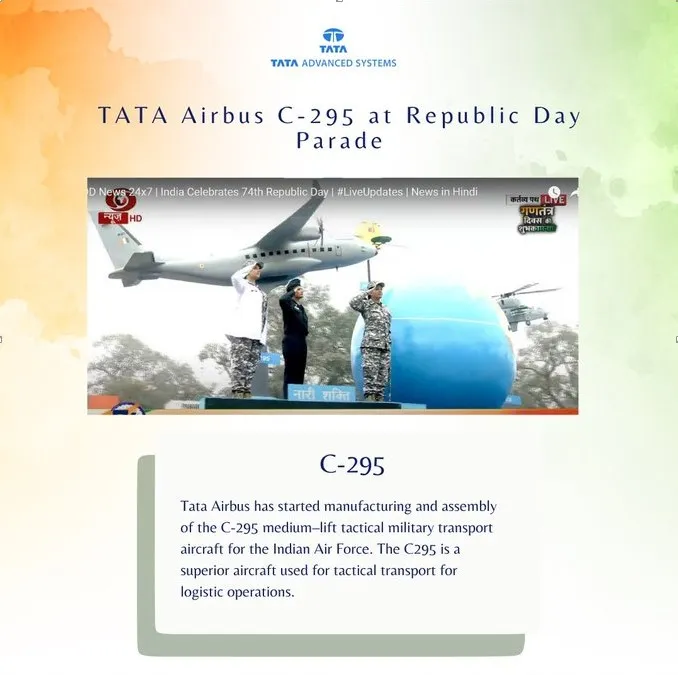
Airbus C295
TASL in collaboration with Airbus will manufacture & assemble medium–lift tactical C-295 transport aircraft for Indian Air Force in India

Tata Boeing Aerospace
TASL's JV with Boeing makes the Apache helicopter fuselage for export to Boeing in the US

Tata Lockheed Martin Aerostructures
TASL JV with Lockheed Martin is the single source of C – 130J empennages globally to Lockheed Martin

Aerostructures and Aero-engines
TASL Aerostructures Division makes the full structure for the entire Pilatus PC12 aircraft, for Global demand


Tata Mine Protected Vehicle
It is fully designed and manufactured in-house and delivers an unmatched combination of proven performance in the harshest operating conditions along with low maintenance and lifecycle cost. The Tata MPV is an “in-service” platform with the Indian Army.

TATA 8X8 WhAP
TASL has indigenously designed and developed, with DRDO, a Wheeled Infantry Combat Vehicle, with amphibious capability. It is an all-terrain and climate system that has been procured by the Indian Army.

Advanced Towed Artillery Gun Systems
TASL has indigenously designed and developed, with DRDO, a 155mm x 52 Calibre Howitzer with maximum range of 45+ Kms. It has an electric drive and is a fully automatic gun that is reliable in all-terrain and climate conditions.

Surface Surveillance Radar
Manufacturing, assembly & integration since 2017 in Defence division, Noida Plant

Missile Launchers
TASL indigenously designs, develops and produces missile and rocket launchers (like Akash, MRSAM, TCT Agni, ULAD, Pinaka) for Indian Armed Forces

Command & Control Systems
Design, Development and Production of Mission Centres and Combat Management Systems


Airborne Platforms and Systems
TASL's Airborne Platforms & Systems Division is developing advanced UAVs

Airbus C295
TASL in collaboration with Airbus will manufacture & assemble medium–lift tactical C-295 transport aircraft for Indian Air Force in India

Tata Boeing Aerospace
TASL's JV with Boeing makes the Apache helicopter fuselage for export to Boeing in the US

Tata Lockheed Martin Aerostructures
TASL JV with Lockheed Martin is the single source of C – 130J empennages globally to Lockheed Martin

Aerostructures and Aero-engines
TASL Aerostructures Division makes the full structure for the entire Pilatus PC12 aircraft, for Global demand














































 to Delhi with the aircraft.
to Delhi with the aircraft.